My experience completing Certified Red Team Operator (CRTO)
0 What is CRTO?⌗
The Certified Red Team Operator (CRTO) certification evaluates and verifies a participant’s ability to simulate adversarial attacks within a Windows Active Directory (AD) environment.
1 Why CRTO?⌗
As a kid, I was always fascinated by hacking and started exploring it at a young age. I became particularly interested in malware development and have been working on it for nearly a decade now.. time really flies. Along the way, I also developed an interest in reading DFIR reports, especially those detailing how ransomware groups compromise entire domains to achieve their objectives.
At one point, I mentioned to a colleague who had already completed the CRTO that I was considering it myself. He encouraged me to go for it. Rather than putting it off, I decided to take the leap and just do it. I’m glad I did.
2 Background & experience⌗
Because of my interest in malware and DFIR reports, I was already familiar with Cobalt Strike. I had even developed my own software for adversary simulations and red team operations. Although fairly rudimentary, it included an implant (or beacon), a team server, and a team client. It was capable of actions such as token theft, lateral movement to other hosts, and using basic profiles for team server customization.
Building this tool gave me valuable insight into what Cobalt Strike is actually doing under the hood, rather than just executing commands to reach a goal. In addition, I spent a significant amount of time on Active Directory machines on Hack The Box (HTB), which helped me better understand the fundamentals of Kerberos attacks before I even considered taking the CRTO.
3 CRTO Course⌗
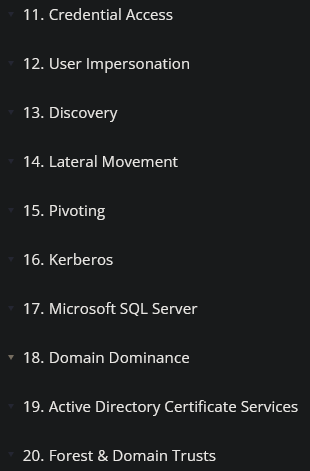
The course is made up of 24 parts, and the first four are purely introductory. They cover legal aspects (particularly UK law, since the CRTO developer is based there), as well as core technical foundations such as malware fundamentals, how Windows processes work, how access tokens function, and how Platform Invoke works in C#.
The Defense Evasion section is probably the most important part of the course, especially in preparation for the CRTO exam. In this section and its accompanying lab, you learn how to evade Windows Defender, which is enabled on all machines in the exam environment; disabling it is not an option. By default, artifacts generated by Cobalt Strike are detected by Windows Defender. This section teaches you how to recompile and modify your own Cobalt Strike artifacts so they can bypass Windows Defender.
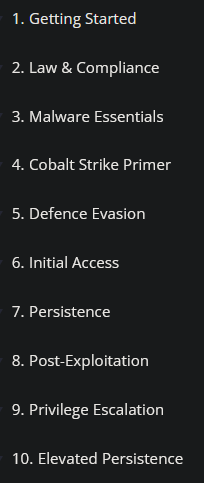
All of the courses below are important to understand. It is not just about knowing the commands, but also about understanding why they work. The Kerberos and MSSQL sections were the most interesting to me.
The Kerberos course goes into a fairly deep explanation of how Kerberos operates, including references to the RFC to explain why certain attacks exist in the first place. Since Kerberos is the backbone of any Active Directory environment, it is important to understand why and when specific attacks work.
That understanding directly benefits your OPSEC as a red teamer, as it helps you avoid generating unnecessary traffic or artifacts while still achieving your operational objectives.
The AppLocker course is also important, as this is a policy you will commonly encounter in real-world environments. Understanding how to interpret it and, in turn, how to bypass it without generating unnecessary noise is crucial for achieving your operational objectives and OPSEC.
4 CRTO Labs⌗
The CRTO courses are accompanied by labs. These labs are designed to guide you through what you need to accomplish to achieve the operational objective, effectively helping you understand both what to do and how to do it.
The labs can only be started once within a 24-hour period, likely to prevent repeated resets and unnecessary resource usage across environments. Each lab also has a time limit, for example; 45 minutes, after which the session ends if you are not finished. In that case, you can attempt the lab again after the cooldown period.
Since the lab environments are largely consistent across the course, a practical way to practice is to redo labs you have already completed, aiming to improve speed and familiarity with the workflow. You can even take on challenges from other labs within these environments, which helps bypass this cooldown timer a bit.
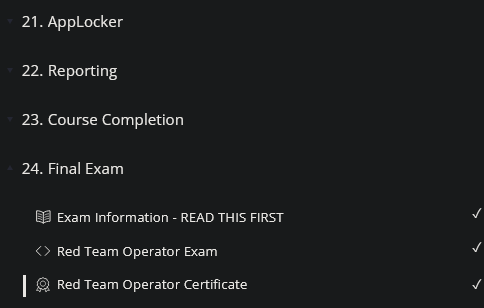
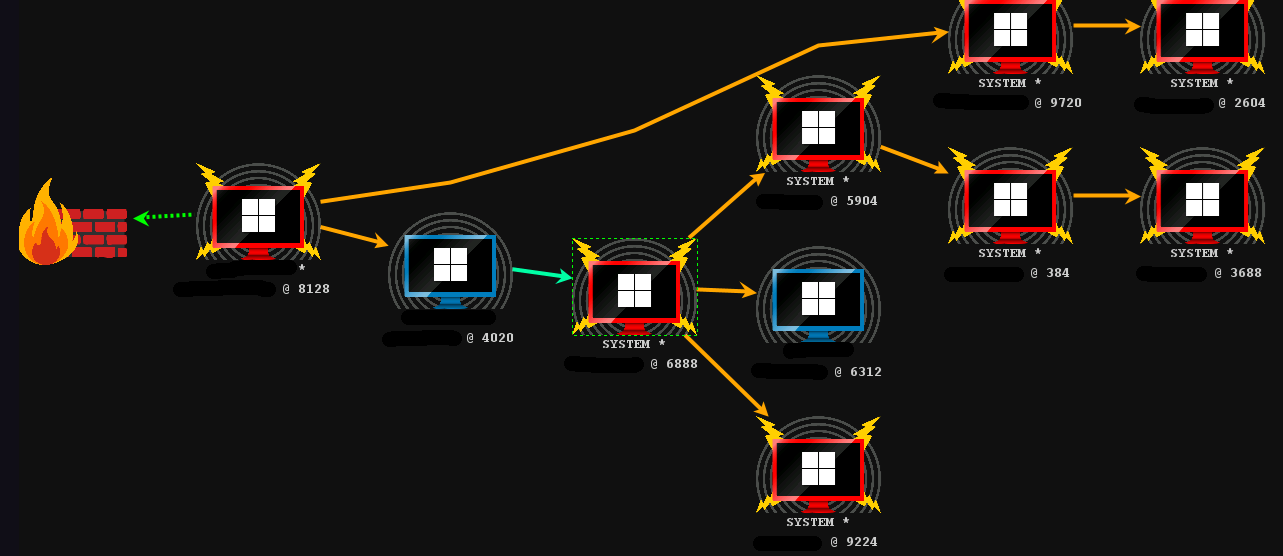
The following image shows an example of how the lab guides you step by step, indicating what you need to do. In my opinion, this is a great way to get introduced to CRTO labs:
5 CRTO Exam⌗
The exam is fun, but it can be challenging if you are not well prepared. My main tip is: if you haven’t already, write everything down in a tool like Obsidian or Notion. That includes commands, expected output (with screenshots), and even your thought process; what to do in different situations and when to do it. This became a major advantage for me during the exam, as I could quickly refer back to my own notes instead of trying to recall everything on the fly.
As part of my preparation, I also created a template with ldapsearch queries to enumerate everything from users, computers, GPOs, OUs, to domain admins.
Enumeration plays a very big role in the exam. If you get stuck, the answer is usually to enumerate more. Is there an OU group that can do something? A user in the domain with useful privileges? A GPO that affects an OU in a way you can leverage?
What the courses did not really cover in depth, but which is highly important, is Cobalt Strike’s malleable C2 profiles. This required me to do additional research into how these profiles work, what capabilities they provide, what configuration options are available, and what each of those options actually does. I did this through the formal Documentation on CobaltStrike.
The exam consists of a total of 100 possible points you can achieve in 24 hours. Achieving the main operational objective (writing to a specific server) accounts for 50 points, but completing this alone is not enough to obtain the CRTO certification. The remaining points are earned by maintaining good OPSEC throughout the engagement. I cannot go into detail about the specific detection rules used in the exam, as that would take away from the experience. However, what is covered in the course is generally sufficient to achieve the operational objective while maintaining acceptable OPSEC standards.
6 Conclusion⌗
I really enjoyed completing CRTO I and I’m also planning to pursue CRTO II. The course content, labs, and exam align well with my background, experience, and interests.
Beyond learning how Cobalt Strike works and which commands can be used to achieve specific operational objectives, I also gained a deeper understanding of why they work. The course encouraged a red team mindset of constantly questioning actions; what a command will actually do, and whether it makes sense for it to originate from a particular process, host, or user context.
Overall, I want to give credit to RastaMouse for putting together such a well-structured and thoughtful course, labs, and exam.